Akhil Bhartiya Cyber Suraksha Sangathan (Regd.)
Regd. with Registrar of Society of NCT Delhi-Regd. No-287
Cyber Criminals se Suraksha, Digital India ki Raksha
अखिल भारतीय साइबर सुरक्षा संगठन (पंजी)
भारत की पहली साइबर क्राइम इन्वेस्टीगेशन एन जी ओ
ऑनलाइन रहें सतर्क, साइबर अपराध से रहें सुरक्षित
www.abcss.org Email: [email protected]

AMIT MALHOTRA
(Cyber Crime Investigation Specialist)
Founder Akhil Bhartiya Cyber Suraksha Sangathan
18 yrs experience in crime prevention, detection and investigation. Certified Ethical Hacker from Ec-Council. Certified Cyber Crime Investigator from Asian School of Cyber Laws. Presently working in the area of cyber crime investigation.
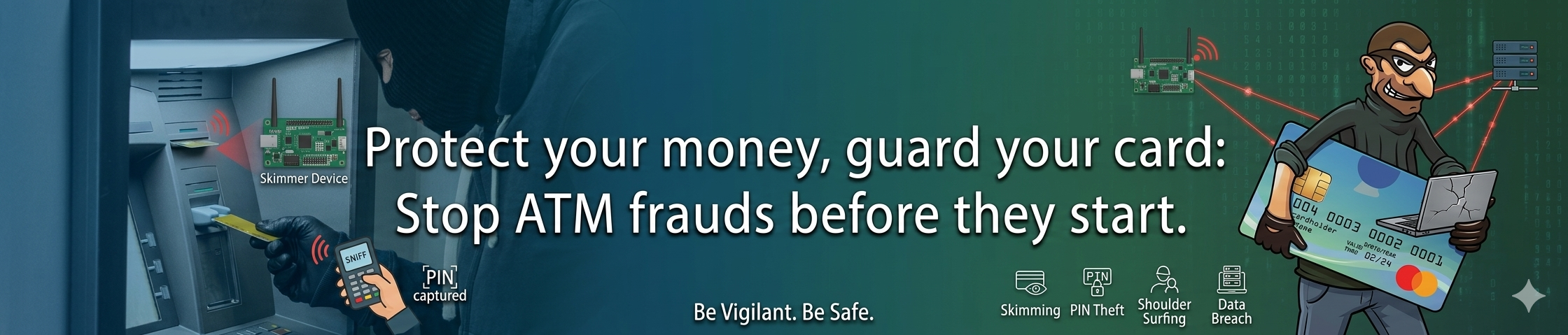
⚠️ Common Methods
- Card skimming devices installed on ATMs
- Fake keypad overlays to capture PIN
- Shoulder surfing at ATMs
- OTP fraud via phone calls (Vishing)
- Card cloning & duplication
- Lebanese loop device to trap cards
- Cash trapping techniques
✅ How to Protect Yourself
- Inspect ATM card slot and keypad before use
- Always cover keypad while entering PIN
- Never share OTP, CVV or PIN with anyone
- Enable SMS alerts for all transactions
- Check bank statements regularly
- Use ATMs in well-lit, monitored locations
- Avoid using ATMs that look tampered with
🚨 If You Are a Victim
- Block your card immediately — call your bank helpline right away
- Call National Cyber Helpline 1930 to report the fraud
- File FIR at nearest Cyber Crime Cell or police station
- Preserve all SMS alerts and transaction receipts as evidence
- Report online at cybercrime.gov.in
- Do not tamper with or delete any digital evidence
Card Skimming
Criminals attach a skimming device on the ATM card slot to read magnetic stripe data. A hidden camera or fake keypad simultaneously captures your PIN.
Vishing (Voice Phishing)
Fraudsters call you posing as bank officials and trick you into revealing your card number, OTP, CVV, or PIN over the phone.
Card Cloning
Using skimmed data, criminals create a duplicate (clone) of your debit or credit card and use it for unauthorized transactions.
Shoulder Surfing
A criminal stands near you at the ATM and watches or records you entering your PIN, then steals or swaps your card.
Lebanese Loop
A plastic sleeve inserted in the card slot traps your card inside. The criminal then retrieves it after you leave, along with your observed PIN.
Cash Trapping
A device is placed over the cash dispenser to prevent cash from coming out. The criminal collects the trapped cash once you leave.
IT Act Section 66C: Identity theft using electronic signatures, passwords or unique identifiers — up to 3 years imprisonment + ₹1 lakh fine.
IT Act Section 66D: Cheating by impersonation using computer resources — up to 3 years imprisonment + ₹1 lakh fine.
IPC 420: Cheating and dishonestly inducing delivery of property — up to 7 years imprisonment + fine.
IPC 468 & 471: Forgery for purpose of cheating and using forged documents as genuine — up to 7 years imprisonment + fine.





